Security Threats
-
People
Invested in cyber training, phishing incidents continue.
-
Process
Invested in process compliances, attack incidents continue.
-
Platform
Invested in advanced technologies, undiscovered attacks continue.
Good Hackers Alliance

Good Hackers Alliance (GHA) focuses on Deep Vulnerability Assessment and Penetration Testing (Deep VAPT) to uncover threats and vulnerabilities that common VAPT service providers fail to identify. Some of the credentials include: winner of world class hacking competitions year after year since 2010, success stories in penetration into critical infra-structures in various large scale and high profile assignments.
Specifically, GHA experts have been helping numerous critical infra-structures such as banks, energy, water, chemical plants achieve world-class level security clearance. One prominent example is, in a consented VAPT assignment commissioned by a governmental ministry, GHA managed to gain control of the gate of a water dam in just 7 hours of indirect hacking from the internet. On references, GHA has over the years established important credentials in penetration testing of planes, cars and industrial control systems; and with that, assisted the customers to achieve high-level assurance of the security postures of their IT and OT operations.
Content De-construction, Neutralization and Re-construction (CDNR)

Today, organizations are not short of choices in advanced cyber protection tools. These mainstream cyber technologies, be it tradition anti-virus, sand-boxing, analytics, machine learning, threat intelligence are all built on the same principle and purpose to detect the bad things and to remove them. Unfortunately, today’s advanced threats are no longer easily detectable. Detection is fundamentally inadequate. It needs to be augmented by non-detection-centric strategy.
In the paradigm of non-detection-centric approach, one of the strategies is sanitization, or popularly known as “Content Dis-arm and Re-construction” (CDR). On this, Athena Dynamics advocates the notion of “Content De-construction, Neutralization and Re-construction” (CDNR) for the simple reason that “dis-arm” has an implicit relation to detection. One needs to detect that there is arm in order to dis-arm it.
CDNR technologies has gained popularity gradually in recent years. Athena Dynamics pioneers the introduction of this fundamentally differentiated cyber strategy to the industries, especially in protection of “crown jewel” assets and Critical Info-Infrastructures of public and private sectors.
Contact Us To Know More About CDNR, and with that, to gain an important perspective that why the mainstream cyber protection approach is far from adequate, regardless of how advanced the technology is.
Pioneering CDR Technologies in 200+ Sensitive Sites since 2010 with Zero Incident

INDUSTRY CONTROL SYSTEMS

PUBLIC SECTOR CLASSIFIED ASSETS

COMMERCIAL SECTOR SENSITIVE ASSETS

DEEP TECHNICAL VAPT
Statistics
150+
PHYSICAL SITES PROTECTED
50+
CLASSIFIED PROJECTS DEPLOYED
60+
PRIVATE CUSTOMERS SERVED
PARTICIPATED IN
40+
CYBER-SECURITY EVENTS
50+
RISK ASSESSMENTS PROVIDED
150+
PHYSICAL SITES PROTECTED
50+
CLASSIFIED PROJECTS DEPLOYED
60+
PRIVATE CUSTOMERS SERVED
PARTICIPATED IN
40+
CYBER-SECURITY EVENTS
50+
RISK ASSESSMENTS PROVIDED

Upcoming & Previous Events
Black Hat Asia | Binalyze speaking session
- 2024 April 18
- 12:55 pm
Upcoming & Previous Events
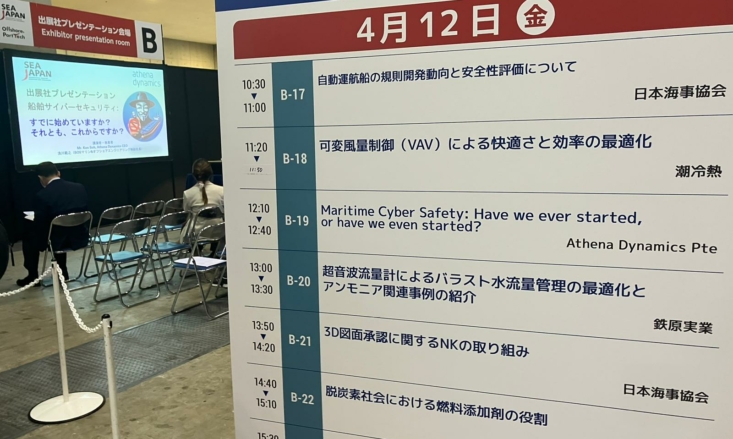
Sea Japan 2024
- 2024 April 10
- 9:00 am
- Tokyo Big Sight

Upcoming & Previous Events
Mastering Cybersecurity in the Digital Supply Chain:Insights and Strategies
- 2024 March 27
- 11:00 am
- Virtual

Upcoming & Previous Events
SSA Tech Show 2024
- 2024 March 22
- 10:00 am

Upcoming & Previous Events
APM 2024: Addressing Emerging Threats and Future Mitigation Strategies
- 2024 March 14
- 12:00 pm
- Sands Expo and Convention Centre

Upcoming & Previous Events
Disruptive Innovations In Cyber Protection: Advancing Thought in the Field
- 2024 March 8
- 11:30 am
- Singapore University of Social Sciences LT A. 4. 07A

Upcoming & Previous Events
3rd SGTech Cyber Security Chapter ExCO
- 2024 March 7
- 4:00 pm
- SG Microsoft Office

Upcoming & Previous Events
Webinar: Modern DFIR Approaches for Effective Malware Investigations
- 2024 February 28
- 3:00 pm
- Online

Upcoming & Previous Events
DICYFOR SECURITY SUMMIT SINGAPORE 2024
- 2024 February 28
- 9:05 am
- voco Hotel, an IHG Hotel

Upcoming & Previous Events
SGTech Members Monday
- 2024 February 5
- 3:00 pm
- SGTech HQ